Hybrid Endpoint Identity Investigation – Windows 11 Study
Date: 5 March 2026
Objective
This laboratory exercise was created as a learning investigation to understand identity telemetry behaviour on a Windows 11 endpoint.
Both Event Viewer inspection and PowerShell audit querying were used to check telemetry consistency.
The main focus was to observe how normal identity activity appears inside security audit logs.
This is a behavioural learning exercise rather than a production security assessment.
Key learning goals:
- Understand authentication signal patterns
- Observe privilege context events
- Evaluate action execution telemetry
- Study session lifecycle signals
Methodology
Identity telemetry was analysed across three observation windows.
Event Signal Classes
| Event ID | Meaning |
|---|---|
| 4624 | Authentication success |
| 4625 | Authentication failure |
| 4672 | Privileged session context |
| 4688 | Process creation |
| 4634 | Session termination |
Data was collected using:
- Windows Event Viewer filtering
- PowerShell audit queries
Temporal Observation Model
- 24 Hours → Behaviour snapshot
- 7 Days → Pattern stability check
- 30 Days → Long-term behaviour view
PowerShell Audit Script
$EventIDs = @(4624,4625,4672,4688,4634)
$Windows = @(
@{Name="24H"; Time=(Get-Date).AddHours(-24)},
@{Name="7D"; Time=(Get-Date).AddDays(-7)},
@{Name="30D"; Time=(Get-Date).AddDays(-30)}
)
foreach ($Window in $Windows) {
Write-Host ""
Write-Host "===== Analysis Window: $($Window.Name) ====="
foreach ($EventID in $EventIDs) {
$Count = (Get-WinEvent -FilterHashtable @{
LogName='Security'
Id=$EventID
StartTime=$Window.Time
} -ErrorAction SilentlyContinue).Count
Write-Host "Event $EventID : $Count"
}
}
Audit Summary
24 Hour Window
- Event 4624 : 166
- Event 4625 : 0
- Event 4672 : 159
- Event 4688 : 13
- Event 4634 : 4
7 Day Window
- Event 4624 : 901
- Event 4625 : 1
- Event 4672 : 863
- Event 4688 : 65
- Event 4634 : 27
30 Day Window
- Event 4624 : 2657
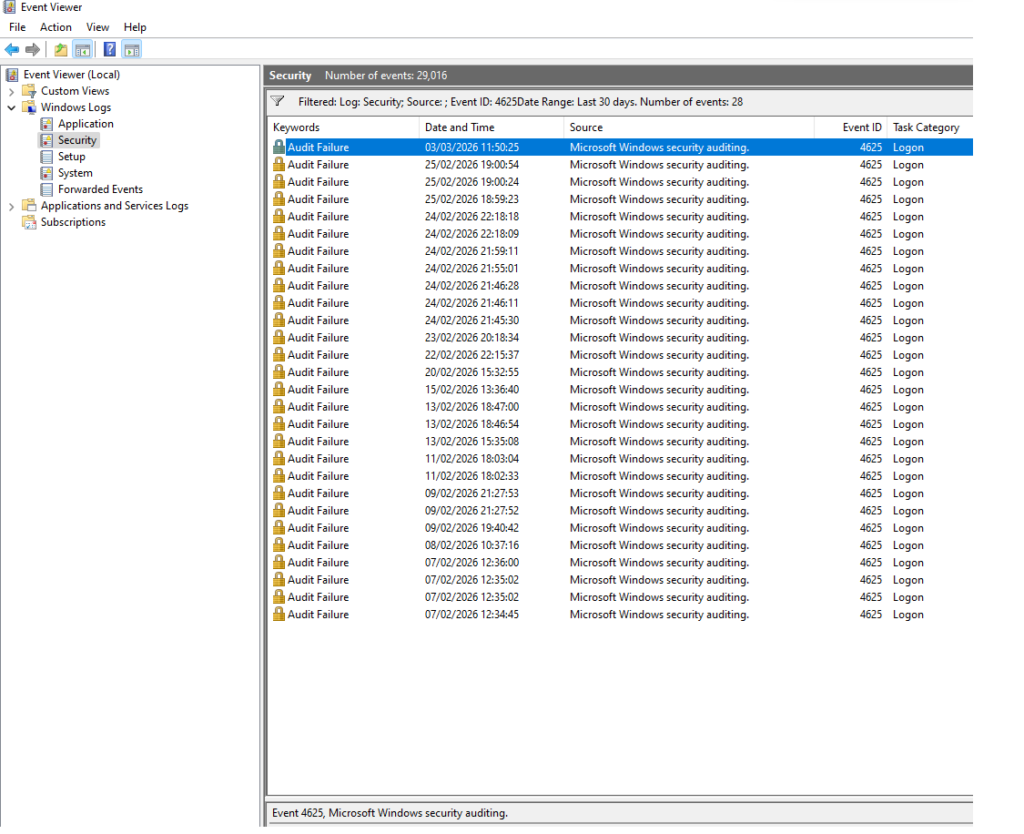
- Event 4625 : 28
- Event 4672 : 2543
- Event 4688 : 156
- Event 4634 : 130
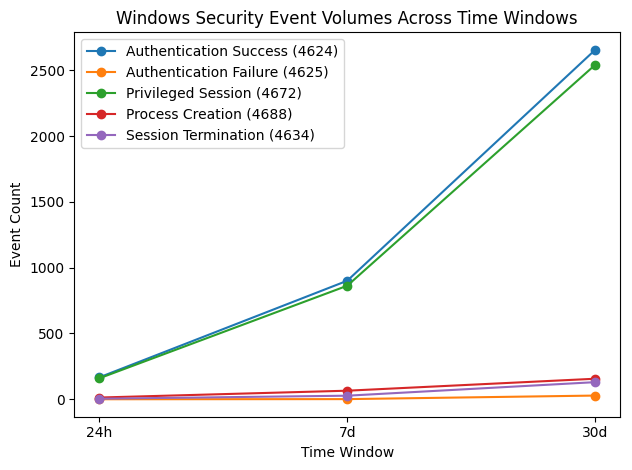
The graph illustrates authentication, privilege assignment, process creation, and session lifecycle signals across observation windows.
Behavioural Ratio Analysis
Raw event counts were normalised into operational indicators commonly used in SOC monitoring.
Privileged Access Ratio
[
Privilege\ Ratio = \frac{Event\ 4672}{Event\ 4624}
]
Measures how often successful logons receive privileged token context.
Observed value:
- Approximately 0.96 across all windows.
Interpretation:
- Administrative or service-oriented usage pattern is likely.
- Privilege assignment behaviour is stable.
Authentication Failure Rate
[
Failure\ Rate = \frac{Event\ 4625}{Event\ 4624}
]
Used to detect credential attack activity such as brute-force or password spraying.
Observed rate:
- Remains below 1% across observation windows.
Interpretation:
- No evidence of authentication abuse signals.
Session Termination Ratio
[
Session\ Close\ Ratio = \frac{Event\ 4634}{Event\ 4624}
]
Measures relationship between session creation and termination behaviour.
Observed range:
- Approximately 2–5%
Interpretation:
- Suggests presence of persistent or background sessions.
- Common in managed workstation or service contexts.
Behavioural Interpretation
Authentication events represent the dominant telemetry signal.
Key observations:
- Privileged context assignment closely follows successful authentication activity.
- Failure authentication events are rare.
- Process execution telemetry volume is relatively controlled.
No clustering or burst-like behaviour patterns were detected within the observation windows.
It is important to note that low event frequency in process creation telemetry may also reflect audit policy configuration rather than true execution activity.
Endpoint → Cloud Security Mapping
Modern security monitoring increasingly operates in cloud-native environments.
Conceptually, endpoint identity telemetry can be compared to cloud audit logging.
| Endpoint Signal | Cloud Security Equivalent |
|---|---|
| Authentication events | IAM login activity |
| Authentication failures | Failed console/API authentication |
| Privilege context assignment | Role assumption events |
| Process execution | Control-plane API operations |
| Session termination | Token lifecycle closure |
Relevant cloud telemetry ecosystems include:
- AWS Identity and Access Management (IAM) monitoring
- AWS CloudTrail audit analysis
SOC Behavioural Conclusion
Across 24-hour, 7-day, and 30-day windows:
- Authentication behaviour is stable.
- Failure signal density is very low.
- Privilege lifecycle behaviour is consistent.
- Process execution frequency is controlled.
Overall assessment:
Endpoint identity telemetry is consistent with normal managed workstation behaviour.
No evidence of anomalous behavioural clustering was observed in the analysed dataset.
Professional Skills Demonstrated
This laboratory exercise demonstrates foundational capability in:
- Behavioural security reasoning
- SOC triage judgement thinking
- Security telemetry interpretation
- Identity-centric detection modelling
- Cloud security conceptual alignment
These competencies are relevant to entry and junior detection engineering roles in UK and EU SOC environments.
Learning Insight
Security investigation should begin by establishing normal behavioural rhythm.
Detection effectiveness improves when anomaly detection is built on well-understood baseline telemetry.
Portfolio Value Statement
This project demonstrates practical understanding of:
- Windows endpoint audit analysis
- Behavioural baseline modelling
- Security log interpretation
- Cloud identity security mapping
- SOC investigative workflow thinking
The approach reflects early-stage detection engineering methodology rather than purely tool-centric analysis.
Executive Summary
This laboratory exercise explored basic Windows identity telemetry behaviour as a learning activity. The analysis focused on understanding how authentication, privilege assignment, process activity, and session lifecycle events appear under normal workstation usage.
The observed logs showed stable behavioural patterns with low failure authentication frequency and consistent privilege context activity following successful logins. While no security anomalies were detected in this dataset, the exercise helped develop foundational skills in security log interpretation and baseline behaviour understanding.
Further learning will focus on improving familiarity with audit policy configuration, telemetry completeness considerations, and methods used in SOC environments to detect deviations from normal identity behaviour.